Bypassing Cloudflare with Browser Automation: A Technical Deep Dive
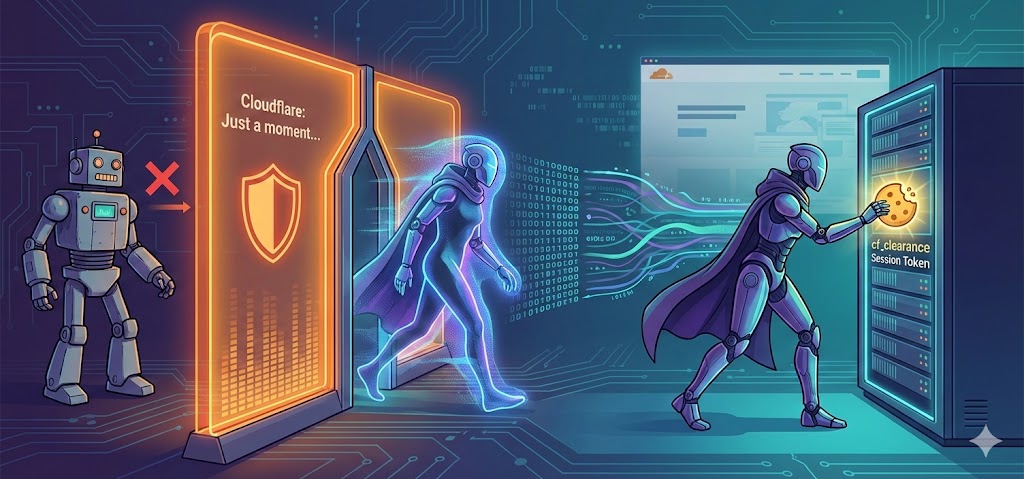
TL;DR: Standard HTTP clients fail Cloudflare checks because they lack real browser fingerprints. The fix is a patched Chromium driver that removes
cdc_strings, overridesnavigator.webdriver, and uses CDP directly. Once the challenge clears, extract thecf_clearancecookie and reuse it with lightweight clients — tied to the same User-Agent and IP.
Note: This guide covers the technical mechanics of bypassing Cloudflare bot protections for educational purposes.
If you’ve tried to scrape a modern website or call an API endpoint, you’ve likely hit the Cloudflare “Just a moment…” screen. Standard HTTP clients like Python’s requests or curl get flagged immediately — wrong TLS fingerprints, no JavaScript execution, and obvious automation variables. To get past Cloudflare’s checks, you need to look like a real browser. The Cereal desktop app handles this complexity internally for scripts that require it — browse the marketplace to see ready-made automation scripts.
The most reliable way to bypass Cloudflare is using an actual browser that has been patched to remove its automation traces.
Why Standard Automation Tools Fail
Standard automation tools like Selenium leave distinct fingerprints. ChromeDriver binaries contain hardcoded identification strings (often starting with cdc_) that Cloudflare scans for and blocks before the page even loads.
Beyond binary signatures, a default browser automation setup reports navigator.webdriver = true to any page-side JavaScript — an immediate indicator of automation. Window dimensions are often unrealistic. User-Agent strings may not match what a real browser would send.
Patched bypass solutions address all of these:
- The
cdc_strings are removed or replaced in the binary navigator.webdriveris overridden to returnundefined- Window dimensions and User-Agent strings are randomized
- Communication happens through the Chrome DevTools Protocol (CDP) directly, bypassing the traditional WebDriver protocol entirely
How the Bypass Logic Works
Once a patched browser navigates to the target URL, the script inspects the page for Cloudflare challenge indicators: titles like “Just a moment…” or “DDoS-Guard”, and HTML elements with IDs like #cf-challenge-running, #challenge-spinner, or #turnstile-wrapper.
If a challenge is detected, the script enters a polling loop — checking the DOM every few hundred milliseconds for two signals:
- The page title changing from the Cloudflare message to the actual site name
- The challenge elements disappearing from the DOM
If the page doesn’t automatically reload within a short window, the script assumes an interactive challenge is present — typically the Cloudflare Turnstile widget.
The Turnstile widget often lives inside an iframe or Shadow DOM to prevent easy access. The script uses CDP to locate the widget’s coordinates and dispatches a synthetic mouse event sequence (move, down, up) to simulate a real click. This usually triggers the final verification step and completes the challenge.
The Prize: cf_clearance Cookie
Once the challenge clears, the goal is to extract the cf_clearance cookie. This cookie is the proof of passage — but it has strict binding conditions:
- It’s cryptographically tied to the specific User-Agent of the browser that solved the challenge
- It’s often tied to the IP address as well
You can’t copy this cookie to a different machine or use it with an HTTP client advertising a different User-Agent. To reuse the session, your lightweight scraper must impersonate the browser exactly — same User-Agent, same cookies — for the duration of the cookie’s validity, which is typically a few hours.
This lets you do high-speed scraping with low-overhead tools like requests or curl without keeping a full browser running for every request.
Technical Reference
Chrome DevTools Protocol (CDP)
CDP establishes a direct WebSocket connection to the browser’s debugging port, bypassing the WebDriver HTTP API entirely.
- Latency: Near-zero for event handling — important when reacting to Cloudflare’s rapid DOM changes
- Control: Low-level access to the network stack for request interception and header modification
- Stealth: No WebDriver binary involved, eliminating a primary detection vector
Binary Patching
cdc_string removal: ChromeDriver binaries contain a static variable key (cdc_adoQpoasnfa76pfcZLmcfl_...). Cloudflare checks for this in the JavaScript context. Patched drivers replace it with a random string of the same length.--disable-blink-features=AutomationControlled: This Chrome flag disables the internal automation indicator that causesnavigator.webdriverto returntrue.
JavaScript Environment Sanitization
Before page scripts run, the automation script injects JavaScript to normalize the browser environment:
navigator.webdriver: Deleted or set toundefinednavigator.plugins: Mocked to return a realistic plugin list (PDF Viewer, etc.) instead of an empty arraywindow.chrome: Ensured to exist with runtime properties expected from a genuine Chrome instance
Turnstile and Shadow DOM Traversal
The Turnstile widget is often inside a Shadow DOM, making standard CSS selectors useless. The solver logic:
- Recursively traverses the DOM, inspecting
element.shadowRootproperties to find the#cf-chl-widget-container - Calculates the center coordinates of the checkbox element relative to the viewport
- Uses
CDP Input.dispatchMouseEventto send a move, mouse-down, and mouse-up sequence — avoiding simple.click()calls, which can be detected as synthetic
Related Tools on Cereal
The TGTG Script on Cereal uses these techniques internally to handle Datadome-protected API endpoints. For a deeper look at the Datadome side, see How to Obtain Datadome Cookies for the Too Good To Go API.